F5 Public Cloud Solutions > 2. Class - PC201 - Deploying F5 Solutions to AWS with Terraform and iControl LX Extensions > 2.2. F5 Admin SSH and Configuration Utility (WebUI) Access Source | Edit on
2.2.1. Check status of F5 instances before proceeding.¶
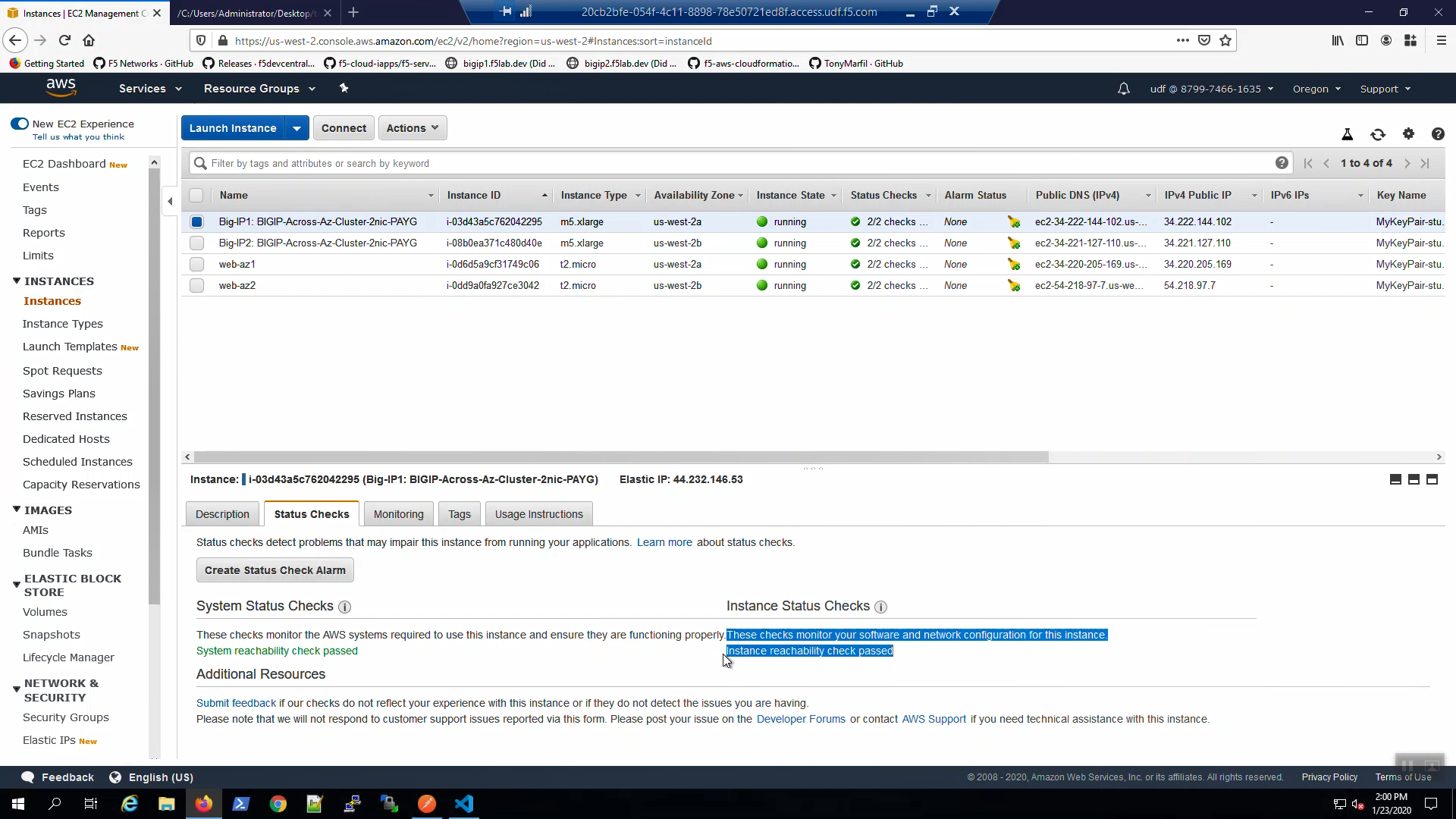
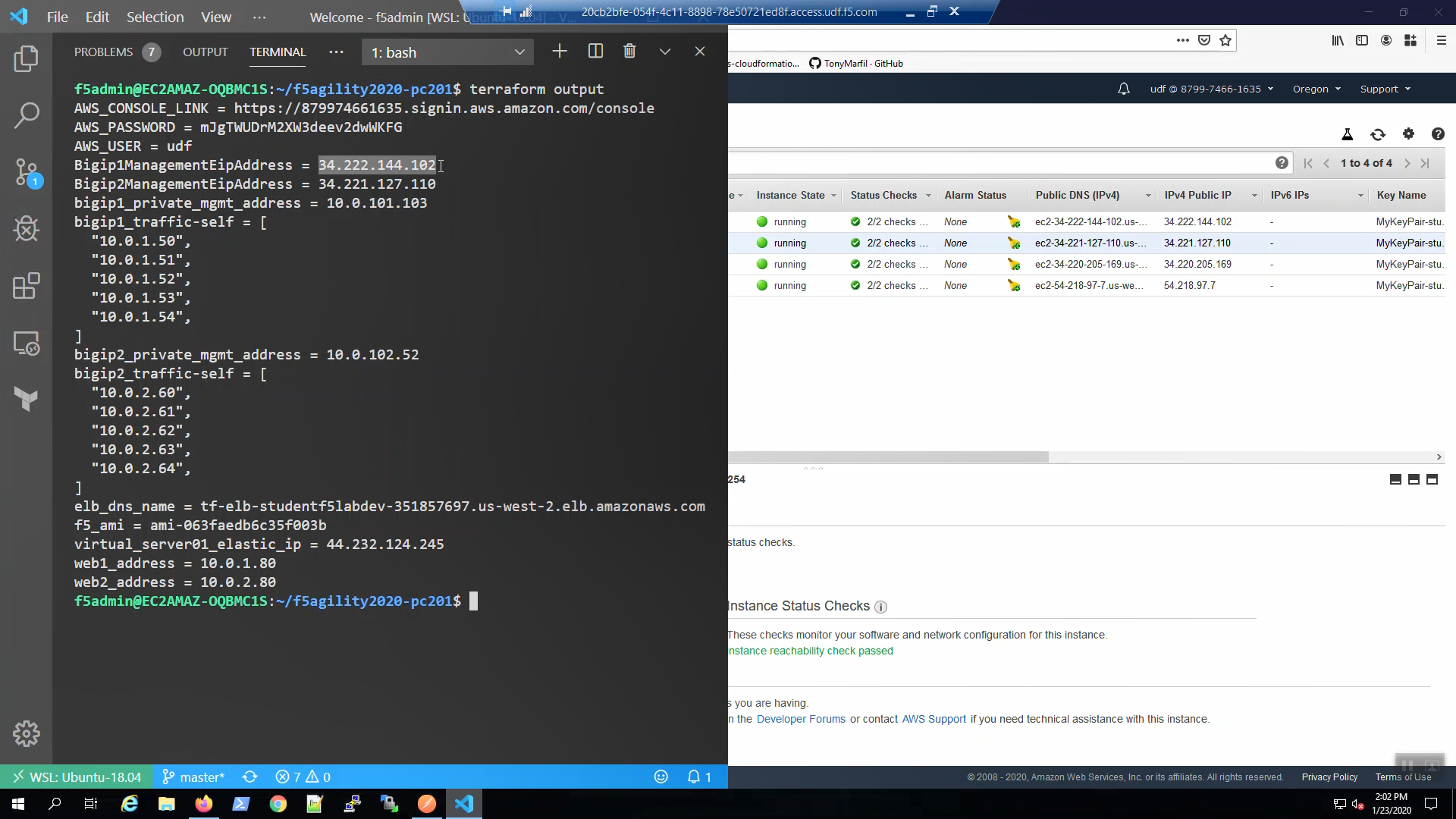
From the AWS Web Console => Services => EC2 => INSTANCES => Instances. Select “Big-IP1…”. Select the “Status Check” tab below.
From the AWS Web Console => Services => EC2 => INSTANCES => Instances. Select “Big-IP2…”. Select the “Status Check” tab below.
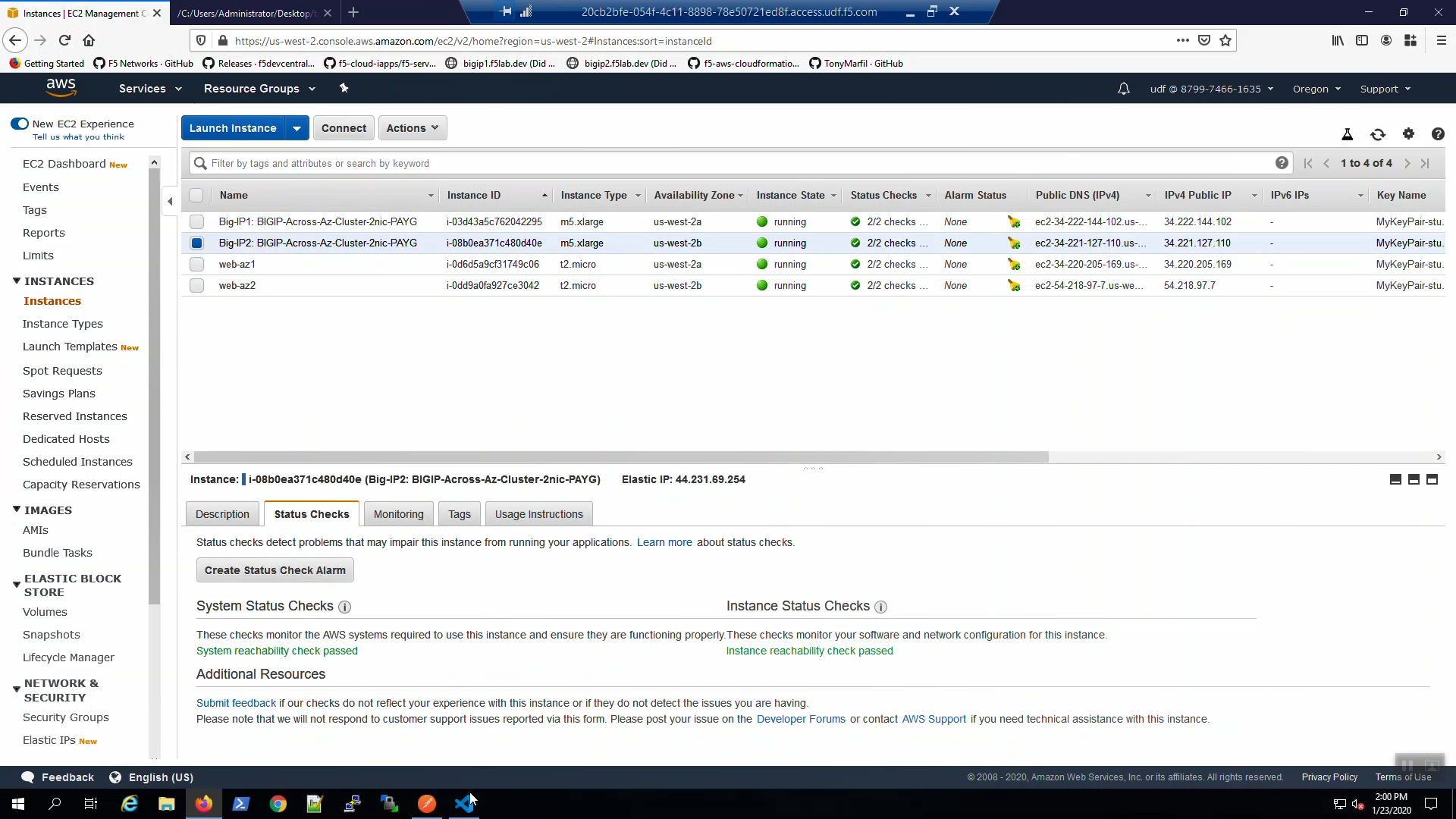
Attention
Do not proceed until both the System Status Checks and Instance Status Checks for both Big-IP1 and Big-IP2 announce …reachability check passed in green!
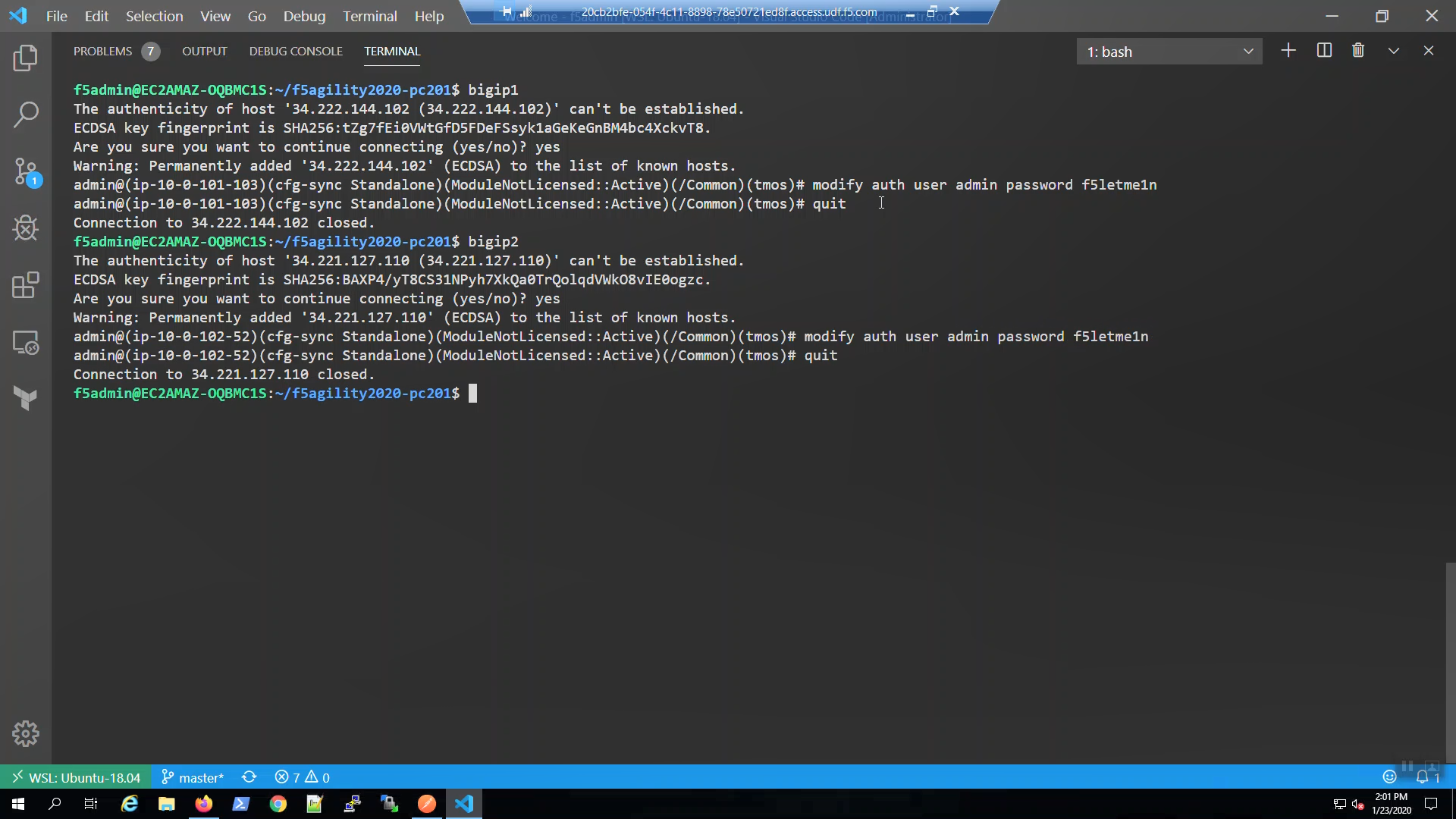
2.2.2. SSH to Big-IP1 and Big-IP2¶
Confirm the bigip1 and bigip2 aliases were created.
type bigip1
type bigip2
SSH to Big-IP1 to confirm state and change the admin password.
Attention
Ensure the system status prompt is either Active or Standby before proceeding. All other status prompts indicate the system is not ready. Use the screenshots as a guide.
bigip1
Acknowledge the ssh remote host when prompted “Are you sure you want to continue connecting (yes/no)?”
yes
modify auth user admin password f5letme1n
modify /sys global-settings gui-setup disabled
save /sys config
quit
SSH to Big-IP2 to confirm state and change the admin password.
Attention
Ensure the system status is either Active or Standby before proceeding. All other status prompts indicate the system is not ready. Use the screenshots as a guide.
bigip2
Acknowledge the ssh remote host when prompted “Are you sure you want to continue connecting (yes/no)?”
yes
modify auth user admin password f5letme1n
modify /sys global-settings gui-setup disabled
save /sys config
quit
2.2.3. Configuration Utility (WebUI) HTTPS access to Big-IP1 and Big-IP2¶
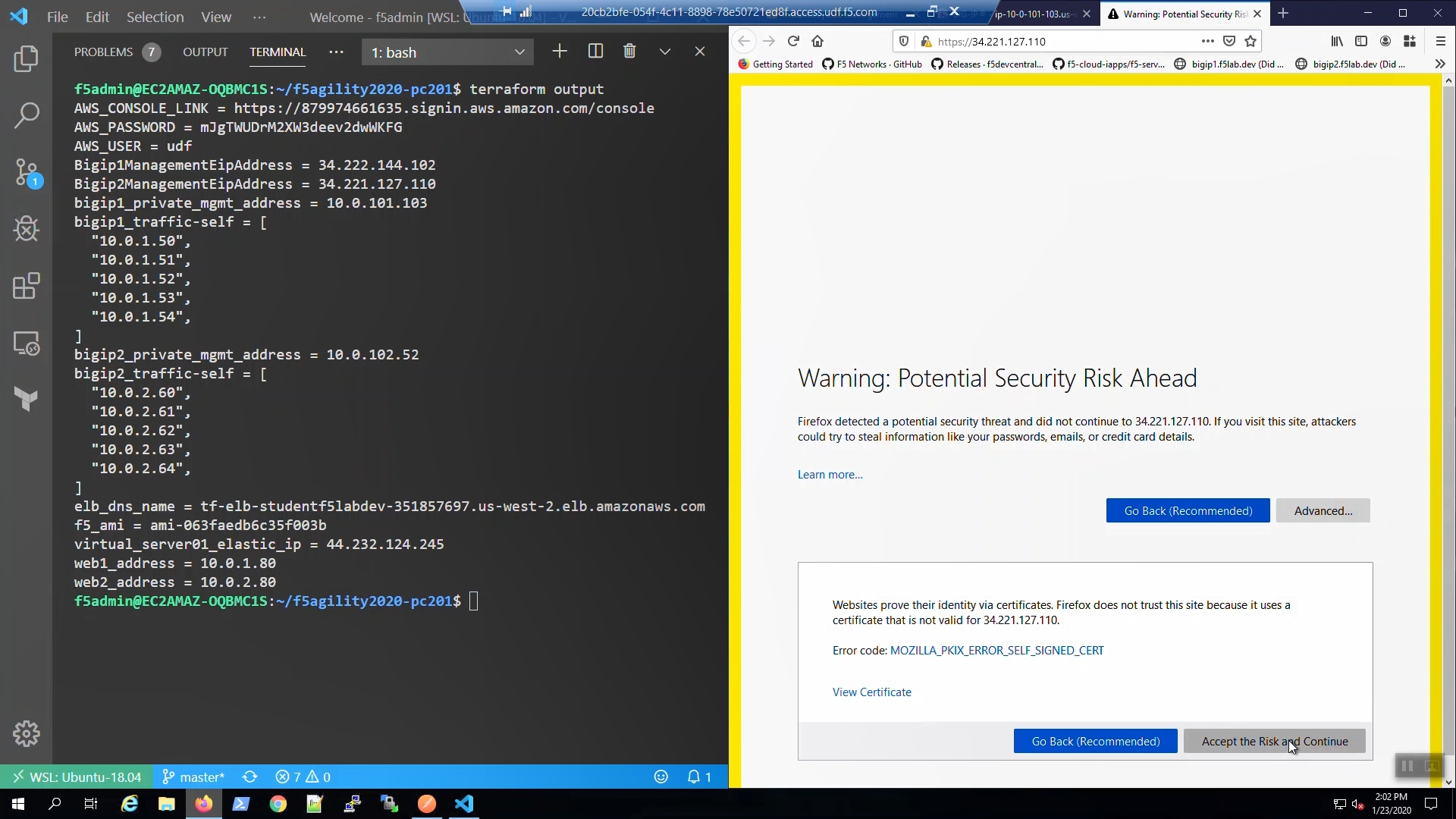
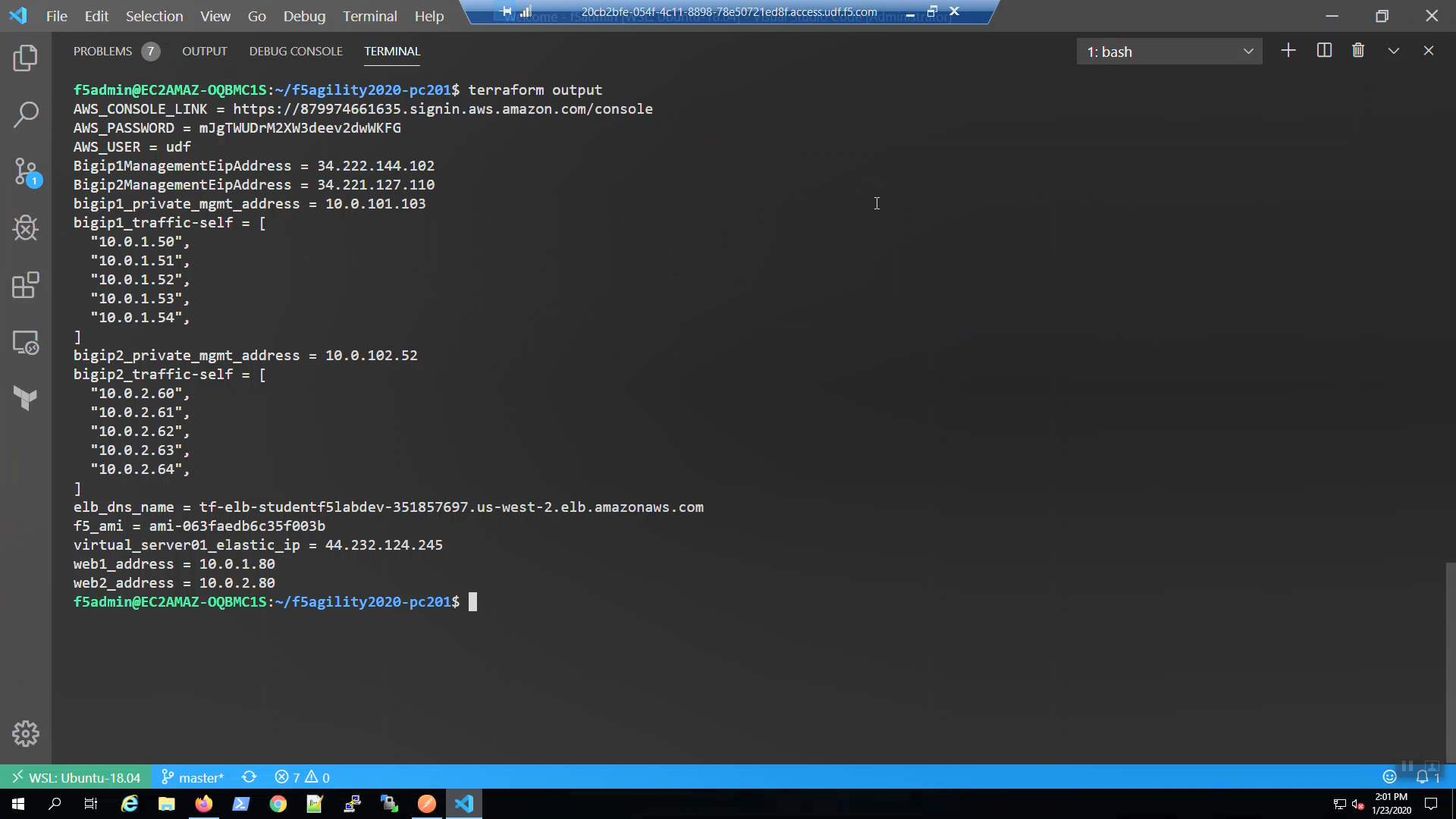
From the Visual Studio Code Terminal, invoke Terraform output. Note the Bigip1ManagementEipAddress and Bigip2ManagementEipAddress values.
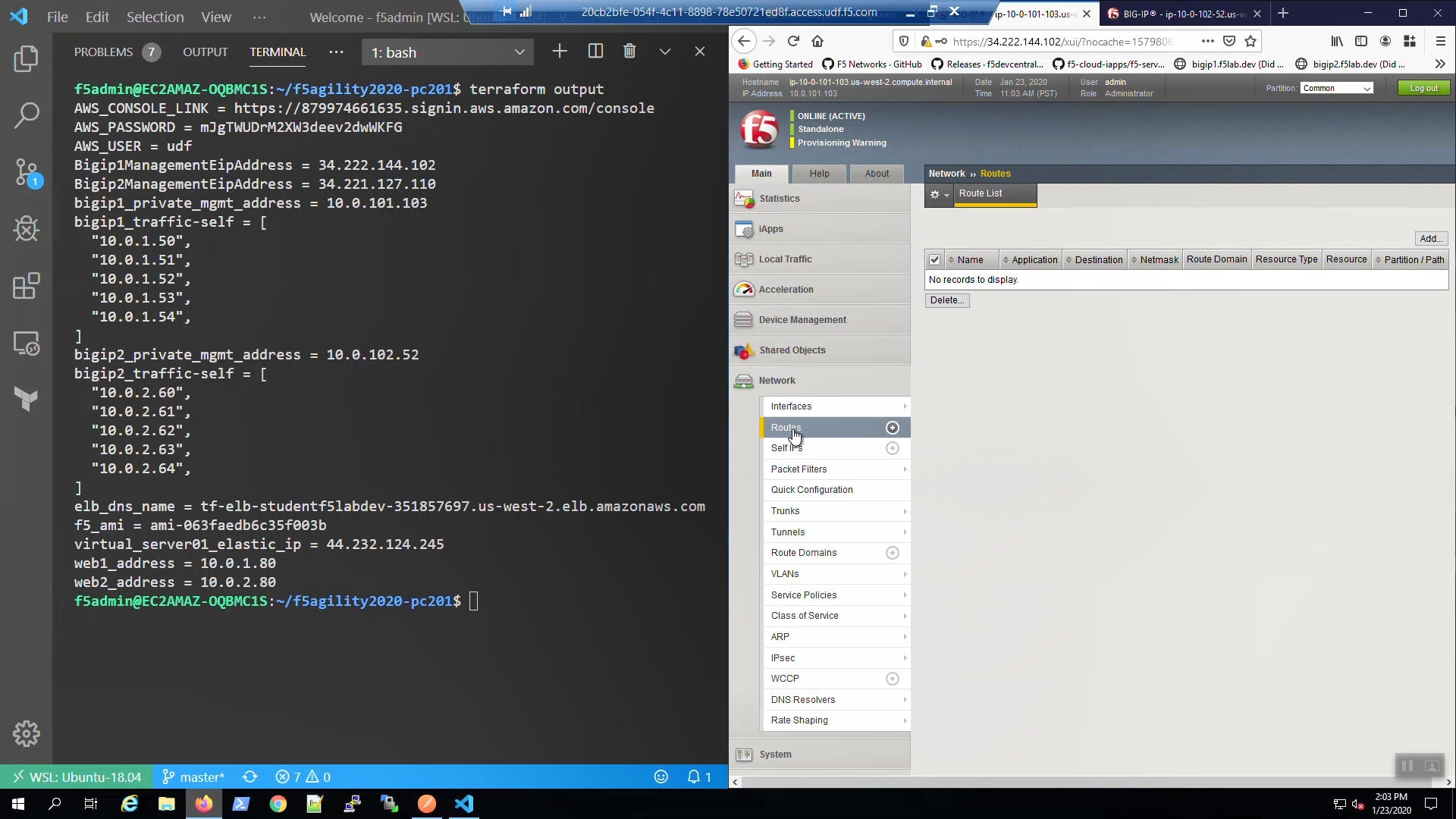
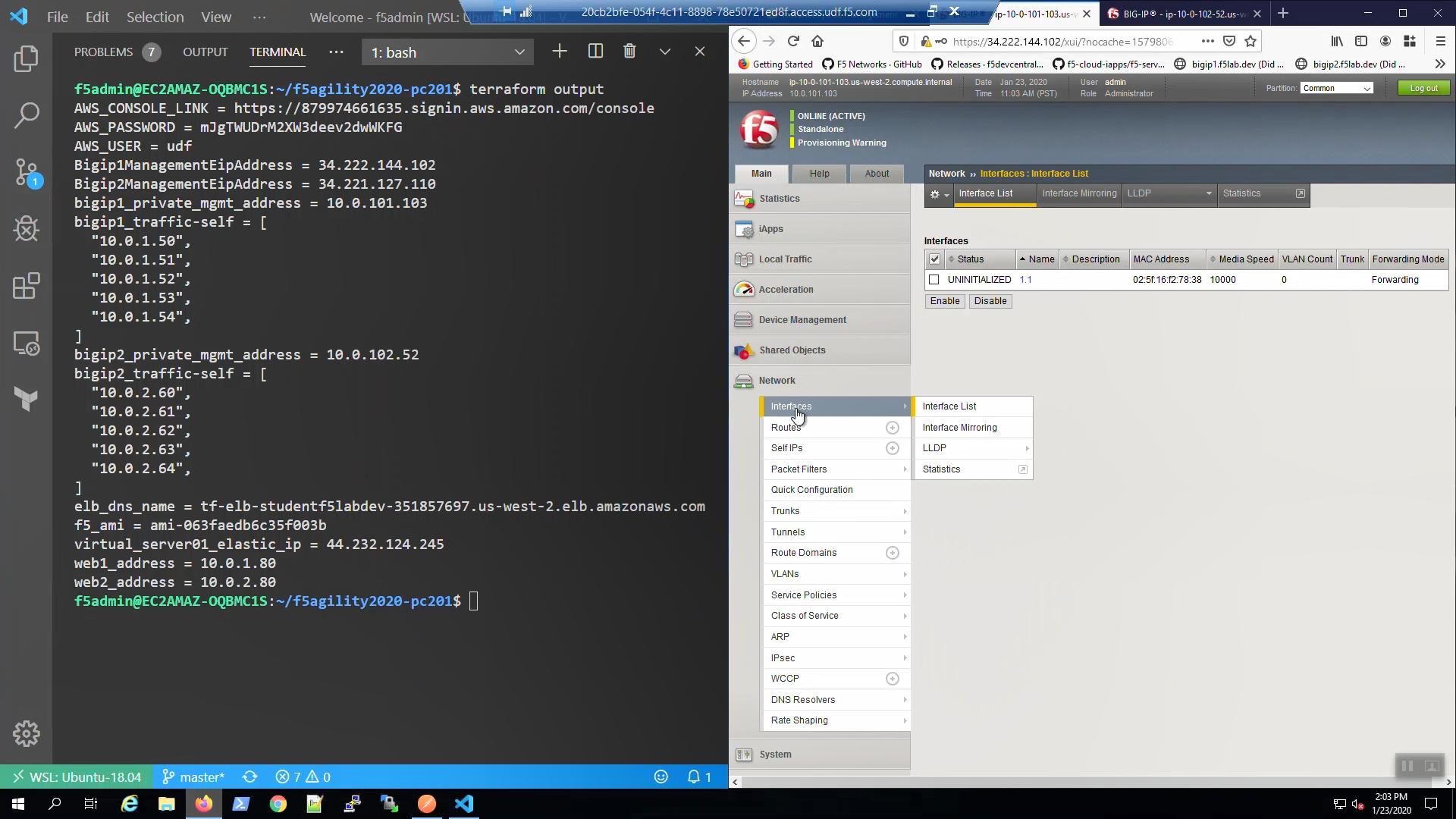
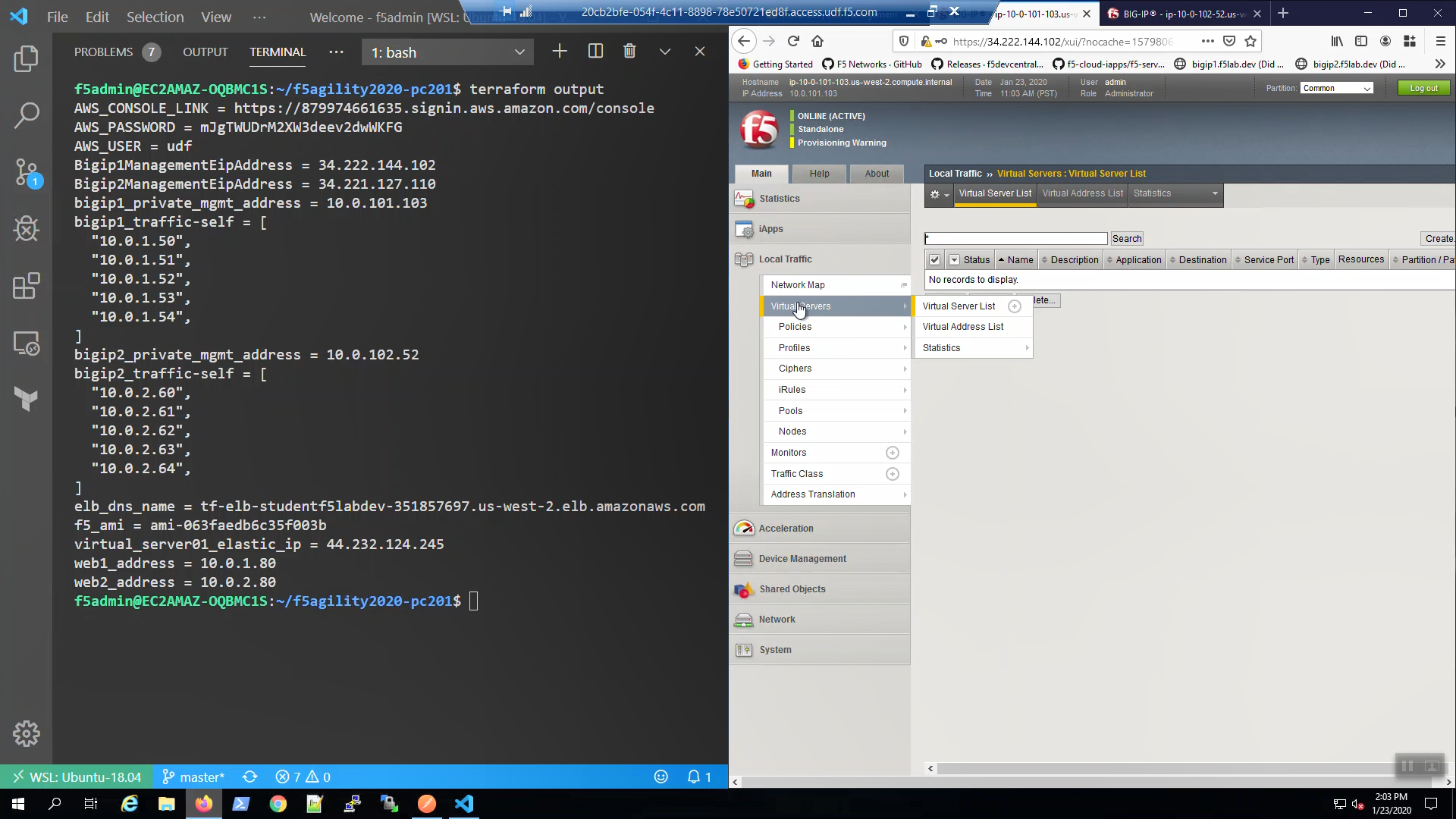
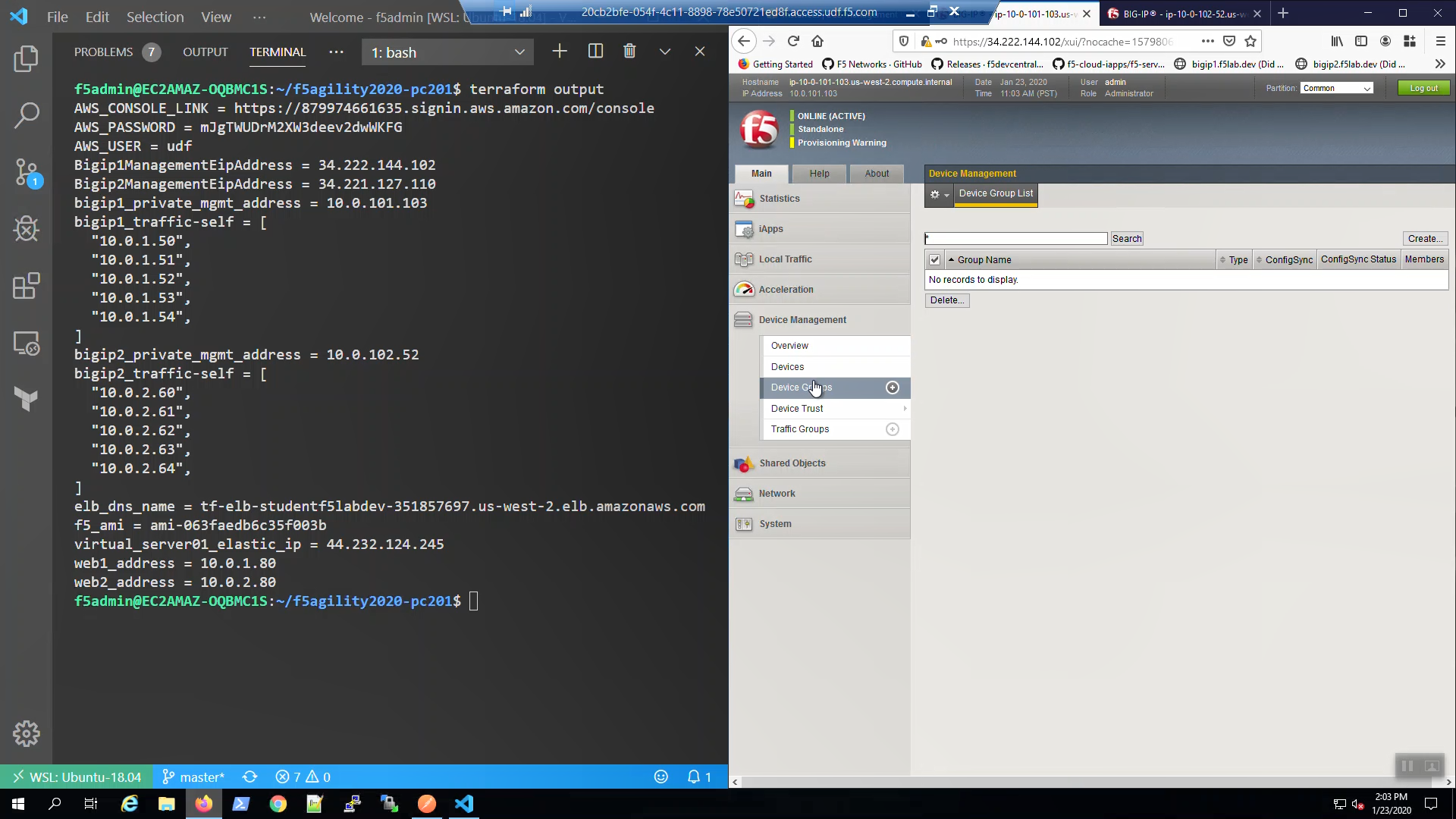
terraform output
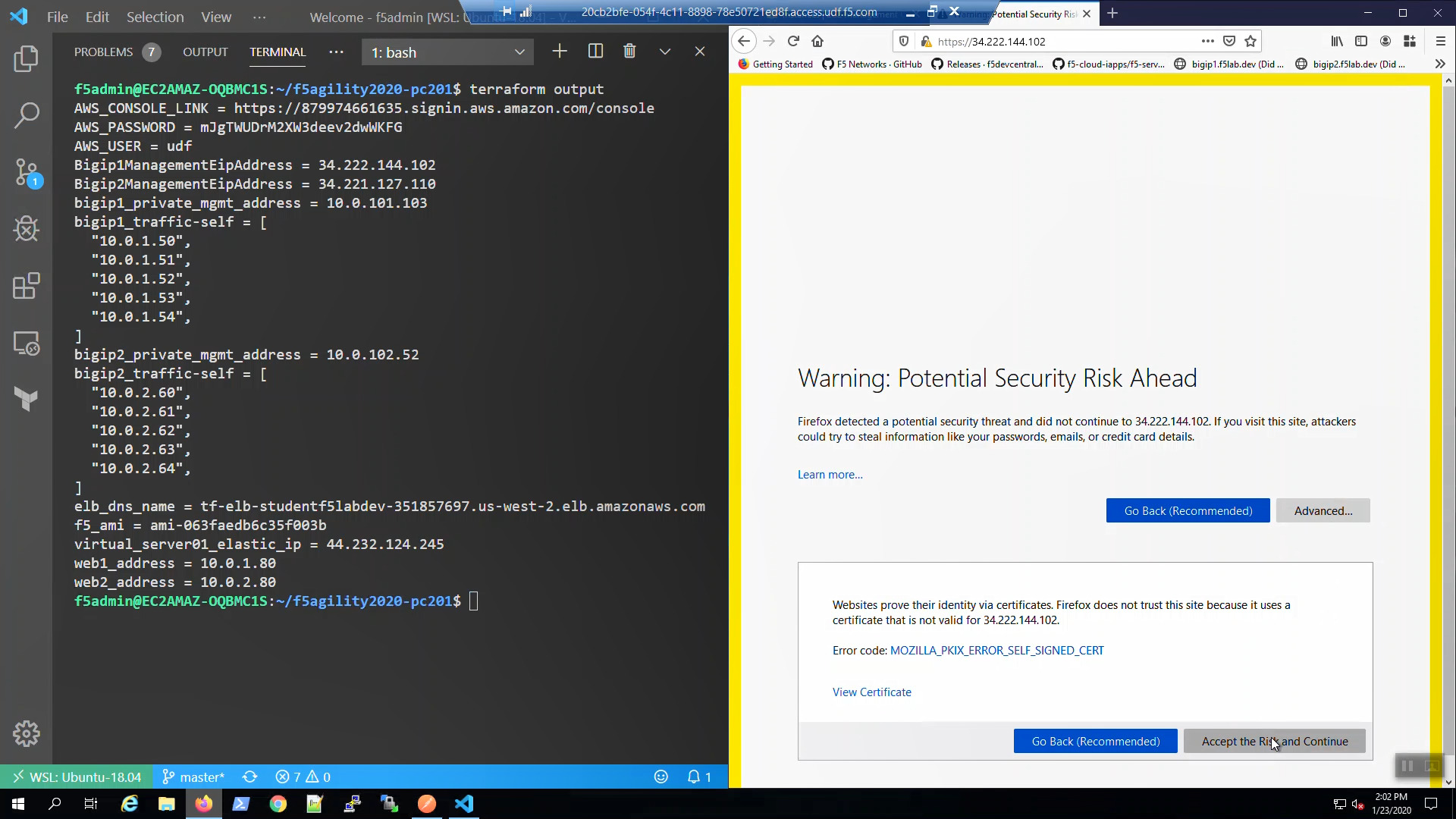
Open a new browser tab and HTTPS to Bigip1ManagementEipAddress. We are using self-signed certificates in the lab. Bypass the TLS warnings. “Accept the Risk and Continue”.
Login to the Big-IP1 Configuration Utility (WebUI):
Username: admin
Password: f5letme1n
…note the system has not been configured with anything other than a management IP address and admin account.
No self-IP.
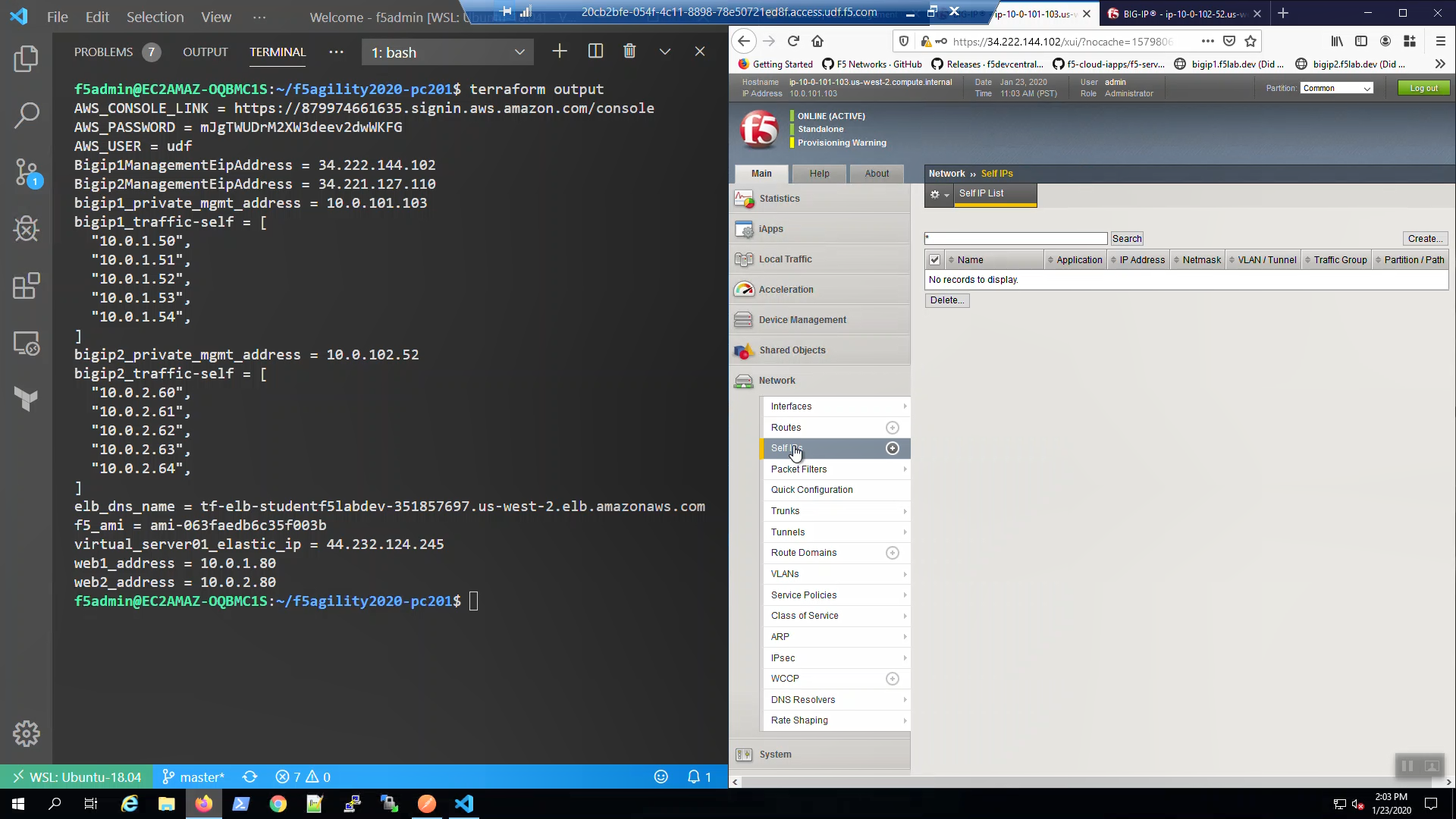
No Routes.
Traffic interface in uninitialized state.
No Virtual Servers.
No Device Groups.
Do the same for Big-IP2.